Microsoft has just announced that they are going to stop trusting any certificate that is signed with SHA-1 algorithm earlier than planned. Microsoft previously made a decision to stop trusting SHA-1 signed codes starting from 1st January, 2017. Today, Microsoft revised their decision and instead of 1st January, 2017, they will start blocking SHA-1 signed certificates from June 2016. The reason for this change is increased threat of successful attacks on SHA-1.
In light of recent advances in attacks on the SHA-1 algorithm, we are now considering an accelerated timeline to deprecate SHA-1 signed TLS certificates as early as June 2016.
Previously Mozilla also made an announcement that they are considering killing SHA-1 certificate support from 1st January, 2017 but they might change the date to as early as July, 2016. Mozilla had planned three actions regarding SHA-1 certificates. 1) To add a security warning to the Web Console to remind developers that they should not be using a SHA-1 based certificates 2) Show the “Untrusted Connection” error whenever a SHA-1 certificate issued after January 1, 2016, is encountered in Firefox and 3) Show the “Untrusted Connection” error whenever a SHA-1 certificate is encountered in Firefox after January 1, 2017. First two actions are already completed by Mozilla and now they are considering to re-schedule the date of stopping SHA-1 support to 1st July, 2016 instead of 1st January, 2017 as planned.
Deprecating support for SHA-1 is not new. Starting from November 2014, Google already begun to ‘gradually sunset’ SHA-1 by displaying a warning in their Chrome web browser on sites whose certificate chains use SHA-1 and are valid past 1 January 2017. These sites are are not considered as ‘fully trustworthy’ in Chrome since version 39.
According to the latest survey done by Netcraft in October, 2015, there are more than one million SSL certificates which are signed with SHA-1 signing algorithm. There are some Certificate Authorities which are still issuing SHA-1 signed certificates despite being considered as insecure. According to the latest research on SHA-1 dubbed as the SHAppening, researchers found that a full SHA-1 collision could be found within 49-78 days on a 512-GPU cluster. Renting the equivalent processing time on Amazon’s EC2 cloud computing service would cost only $75k-$120k. This research points towards an alarming fact that the SHA-1 collision can take place way before 2018 as previously estimated. The internet industry’s plan to deprecate SHA-1 by 2017 might not be fast enough according to the research.
SHA-1 has been proven prone to attacks since way back in 2005. With the increasing threat of successful SHA-1 attacks in near future, the decision to retire SHA-1 earlier than projected is welcomed. SHA-2, the successor to SHA-1 is already pacing ahead. According to Netcraft, the rate of SHA-2 growth increased in the wake of the 2014 HeartBleed bug. This bug resulted in around half a million certificates being potentially compromised, requiring urgent reissuance and revocation.
If you are a webmaster currently using SHA-1 signed SSL certificates, you should consider moving to SHA-2 (SHA-256 variant) as soon as possible before the situation gets worse for your website. If you are planning to get a certificate signed, you must opt for SHA-2 signed certificates. If the CA (Certificate Authority) does not support SHA-2, you should consider moving to the next CA.
If you are a user browsing websites and providing any personal or financial detail to a website, you should make sure the website is using SHA-2 certificate. Be very cautious while using any financial or e-commerce website which is still using SHA-1 certificates.
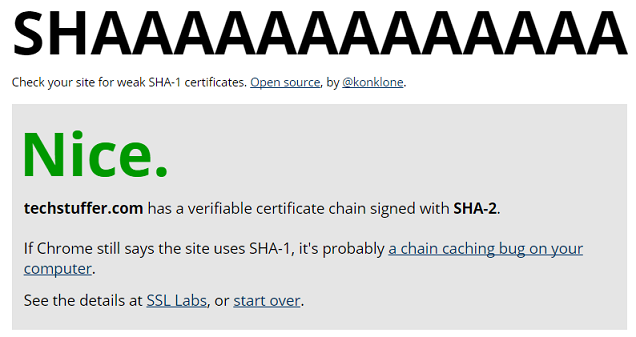
SHAAAAAAAAAAAAA, an open source project by Eric Mill can check a URL for weak SHA-1 certificates. You should enter a URL to check if it is using SHA-1 or SHA-2 certificates.
I hope you found this article informative and I’d like to thank you for reading.
Until we meet next.
Support Me: If this article/tutorial helped you today, please consider supporting me and help me run frunction.com